Vérification de la sécurité au niveau de l’entreprise
Nos clients sont très attachés à la sécurité et nous le sommes aussi. Nextcloud s’aligne sur les normes industrielles telles que la clause 14 de la norme ISO/IEC27001-2013 et les normes, orientations et principes de sécurité connexes. Notre solution s’articule autour de plusieurs niveaux de sécurité, à savoir des fonctions de sécurité étendues, l’application des meilleures pratiques régies par une politique et la conception elle-même validée par des processus de test conformes aux normes de l’industrie.
Suivi et pilotage
Autorisations
Conservation des données
Contrôle d'accès aux fichiers
Cryptage multicouche

Conformité
Intégration
Stockage
Nextcloud prend en charge votre solution de stockage existante, en gardant les données sous le contrôle d’administrateurs informatiques de confiance et gérées selon des politiques établies. Nextcloud fonctionne avec des bases de données SQL standard comme PostgreSQL, MySQL et MariaDB pour le stockage des utilisateurs et des métadonnées.
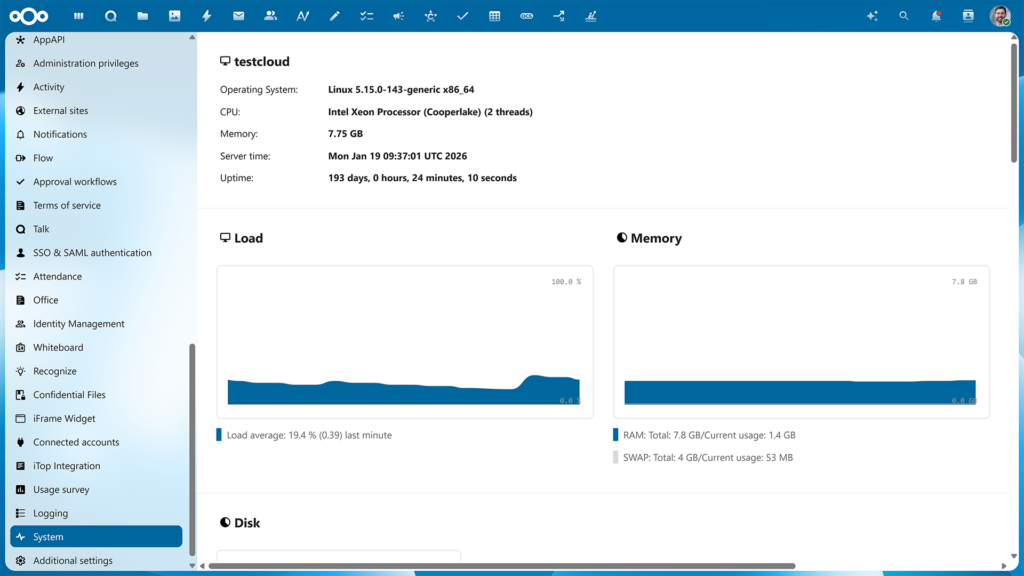
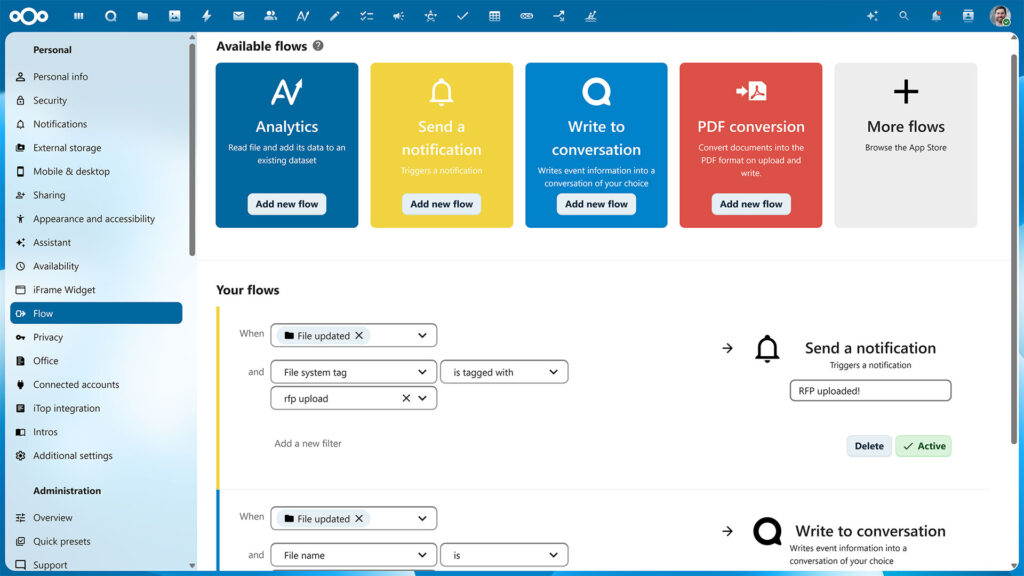
Contrôle
Nextcloud offre des outils de pilotage intégrés et s’intègre aux outils existants de MDM, DLP, d’enregistrement des événements et de sauvegarde, ce qui permet d’utiliser les chaînes d’outils existantes pour contrôler, sauvegarder et restaurer les systèmes.
Le service informatique aux commandes
Nextcloud s’appuie sur les technologies existantes de stockage de données et de bases de données, de sorte que les politiques de sécurité et les processus de gouvernance actuels peuvent continuer à être utilisés pour gérer, contrôler et sécuriser les opérations avec la plateforme Nextcloud. Votre service informatique est entièrement aux commandes.
Études de cas sur la sécurité
Examen de la sécurité par NCC Group
Nextcloud comprend la nécessité de répondre aux exigences fondamentales en matière de sécurité.. En tant que tel, Nextcloud est construit sur ces principes de sécurité afin d’offrir une solution robuste à ses clients.
Audit du code Nextcloud par Swiss Kyos
La deuxième ville de Suisse, Genève, a demandé à la société suisse de sécurité informatique Kyos d’auditer la base de code Nextcloud qu’elle utilise.
Mesures de sécurité passives
Outre les mesures de sécurité actives telles que l’authentification et le cryptage, Nextcloud protège vos données sans qu’aucune action de l’administrateur ne soit nécessaire.
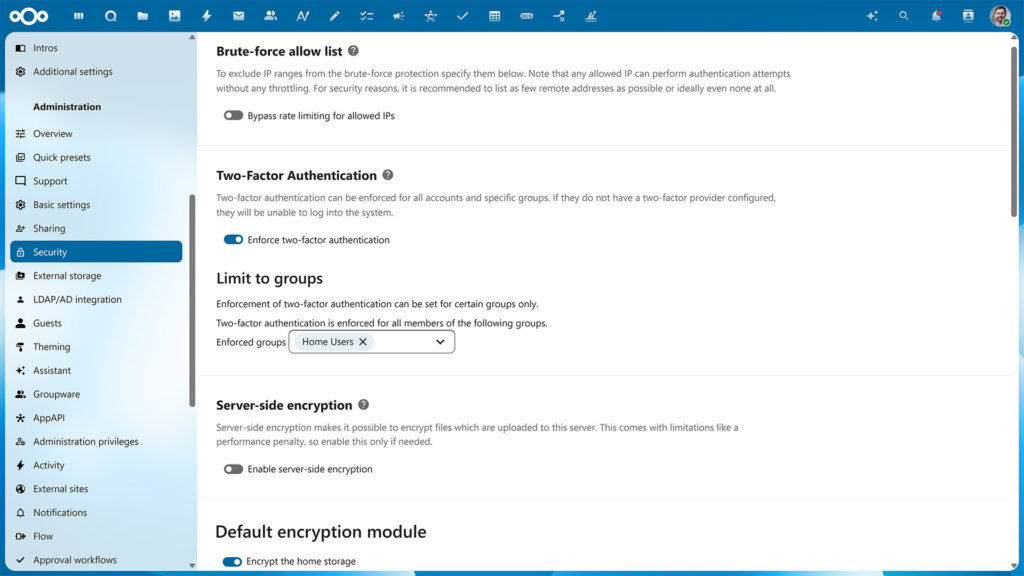
Protection contre la force brute
Limitation du débit

Détection des connexions suspectes basée sur l'apprentissage automatique
Renforcement de la sécurité
Nextcloud utilise un large éventail de dispositifs de renforcement de la sécurité, notamment :
Content Security Policy 3.0
CSP est une fonctionnalité HTTP qui permet au serveur de définir des restrictions spécifiques sur une ressource lorsqu’elle est ouverte dans un navigateur. Par exemple, n’autoriser le chargement d’images ou de JavaScript qu’à partir de cibles spécifiques.
La norme CSP 3.0 est la version la plus récente et la plus stricte de la norme, ce qui accroît la difficulté pour les pirates d’exploiter une vulnérabilité de type « Cross-Site Scripting ».
Cookies SameSite
Les cookies SameSite sont une mesure de sécurité prise en charge par les navigateurs modernes qui empêchent les vulnérabilités CSRF et protègent davantage votre vie privée. Nextcloud veille à ce que les cookies SameSite soient présents sur chaque demande en imposant cette règle au sein de l’entrepôt intermédiaire de la demande.
Nous incluons le préfixe __Host dans le cookie (si le navigateur et le serveur le supportent). Cela permet d’atténuer les vulnérabilités liées à l’injection de cookies dans d’éventuels logiciels tiers partageant le même domaine de deuxième niveau.
Renforcement de la sécurité des mots de passe
La sécurité des mots de passe est extrêmement importante et Nextcloud suit les normes les plus récentes et les plus strictes.
Nous allons au-delà de ces normes, en vérifiant les mots de passe par rapport à la base de données de comptes et de mots de passe compromis du célèbre chercheur en sécurité Troy Hunt. Cette fonction facultative mais fortement recommandée permet de s’assurer que les utilisateurs ne peuvent pas réutiliser un mot de passe qui a déjà été compromis sur un autre site web. Lisez notre blog pour savoir comment cette fonctionnalité protège les utilisateurs.
Authentification
Protection active et passive
Nextcloud offre une série de fonctions de sécurité avancées :
- Cryptage côté serveur, côté poste client et en transit
- Renforcements de sécurité tels que la détection de la force brute, le CSP et le SCC
- Détection des connexions suspectes basée sur l’apprentissage automatique
- Contrôles de sécurité et avertissements automatisés
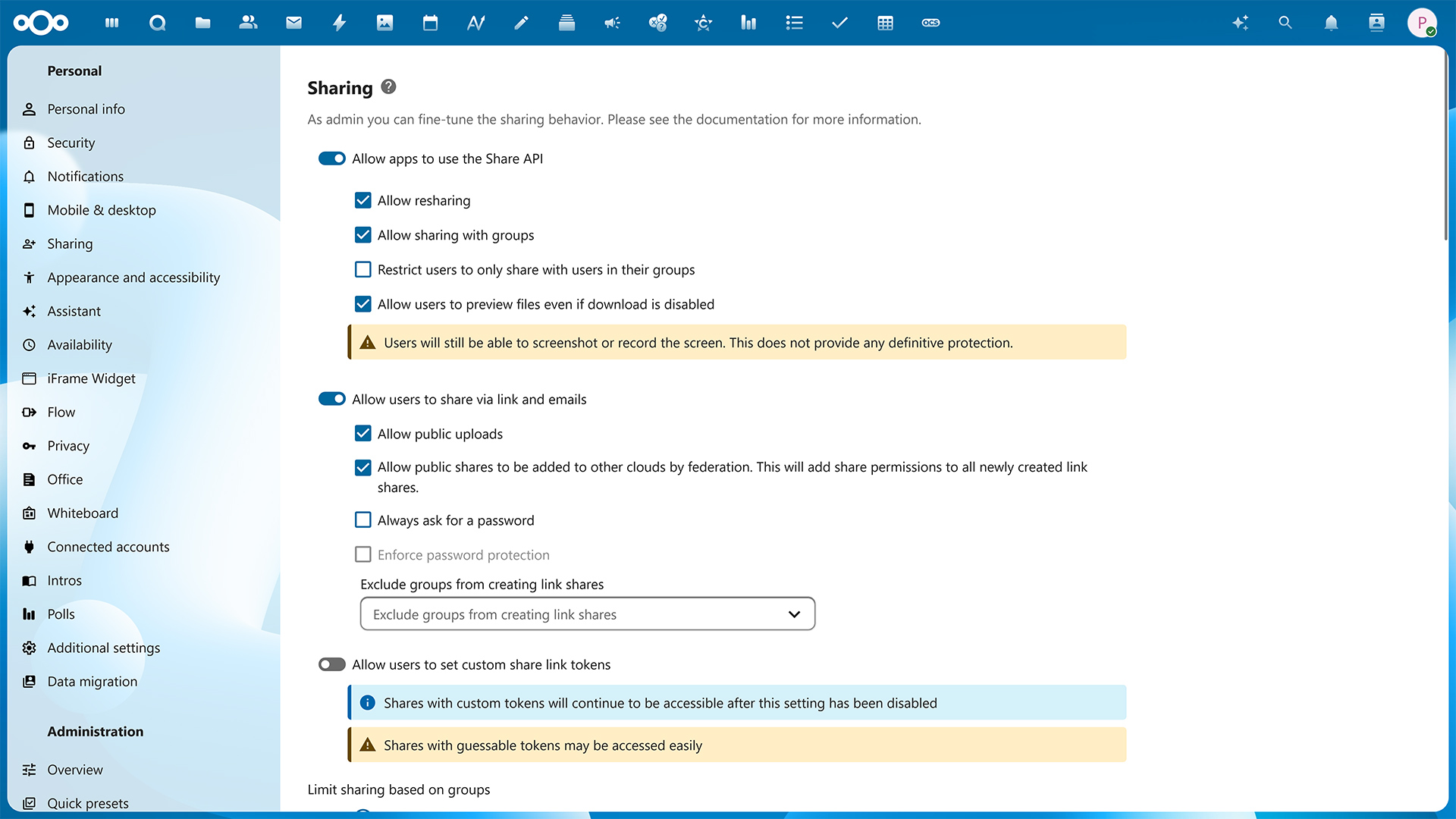
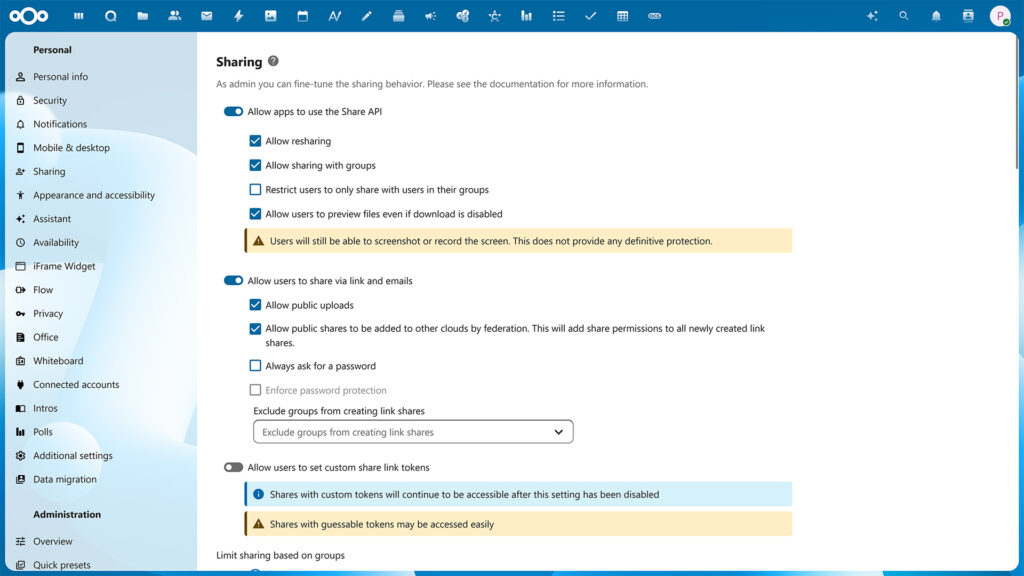
Partage protégé
Pour les clients de Nextcloud, la sécurité des échanges de données est essentielle. Nextcloud offre des mécanismes de protection standard et ajoute des capacités innovantes et uniques telles que la vérification vidéo.
Sécurisation des liens partagés
Nextcloud offre une protection de premier ordre pour les partages de fichiers.
- Partager le mot de passe
- Date d’expiration
- Droits d’accès (lecture/écriture, re-partage)
- Masquer le téléchargement (Affichage sécurisé)
- Masquer la liste des fichiers (Dépôt de fichiers)
- Contrôle de l’accès aux fichiers
- Vérification vidéo
- Les administrateurs peuvent définir des valeurs par défaut ou appliquer ces options.
Vérification vidéo
Dans des situations où une sécurité extrême est justifiée et où l’identité d’un destinataire doit être vérifiée avec une certitude absolue avant qu’il ne reçoive l’accès, Nextcloud inclut la mise en œuvre de la vérification vidéo, une première dans l’industrie.
La vérification vidéo impose un appel vidéo Nextcloud Talk avant que l’accès ne soit donné à un partage, en s’assurant que l’identité du destinataire est correctement vérifiée. L’appel peut être pris via les applications Nextcloud Talk Mobile et l’interface web.
Suppression à distance
Bien que Nextcloud prenne en charge les solutions de gestion des appareils mobiles, grâce à une prise en charge intégrée, la suppression à distance fonctionnera sur les systèmes qui ne sont pas gérés par l’entreprise. Cette fonction est utile pour les utilisateurs privés, mais aussi pour les grandes universités et, bien sûr, dans le cas où les comptes des invités sont confiés à un tiers. Si vous autorisez le téléchargement de documents par des tiers, vous pouvez effacer les documents de leurs appareils lorsque la collaboration est terminée.
La suppression à distance peut être utilisée pour chaque appareil par les utilisateurs et pour chaque utilisateur par l’administrateur.
Espace virtuel de données
Dans les cas où un pare-feu est nécessaire entre les départements ou les organisations sans entraver une collaboration fluide et efficace, un espace virtuel de données distinct peut être mis en place. Nextcloud offre une large gamme de fonctionnalités uniques pour l’utilisation de la VDR (Virtual Data Room) et sa nature sur site offre une confidentialité et un contrôle inégalés.

Reprendre le contrôle
Protégez vos données et vos communications grâce à la principale plateforme collaborative de gestion de contenu. Contactez-nous dès maintenant pour savoir comment nous pouvons vous aider !